Chair’s letter in the annual Multicast newsletter:
It is my pleasure and honor to succeed Michael Scott as the chair. We are an elite research department in a private university that excels in undergraduate education and advanced research. Our faculty size, 21 tenure track and 6 instructional, is substantial in size to lead research and teaching across broad topics in AI/HCI, systems, and theory, yet small enough to operate by consensus. This combination of size and strength is unique, making it the best department for me for over two decades. My goal for the three-year term is to maintain its quality, spirit, and momentum.
This is the year the department turns 50 and simultaneously grows young again. The department has grown steadily under Michael’s stewardship in the past four years, and Sandhya Dwarkadas’s before that. For the first time in over two decades, junior faculty outnumber senior faculty. The staff size is at an all-time high, and most administrative staff are recent hires.
As part of the Meliora weekend, we celebrated our 50th anniversary with morning talks, an afternoon meet-and-greet, and an evening reception at the Hawkins-Carlson room at the library. Registration was beyond capacity for all three events, and the evening cocktail party was standing-room-only with a full house. Thanks to all who came to the celebration, especially our four keynote speakers: Danny Sabbah reminisced about how he fell asleep in his breakfast bowl after the grueling first-year exams; Amanda Stent defined modern AI as solving problems unsolvable by algorithms and then took questions for 24 minutes; Chris Stewart was as inspiring in his work, digital agriculture, as he was to me when he was in my advanced compiler class; and Michael Scott more than anyone embodied the department’s distinguished identity and stature, with grace and humor.
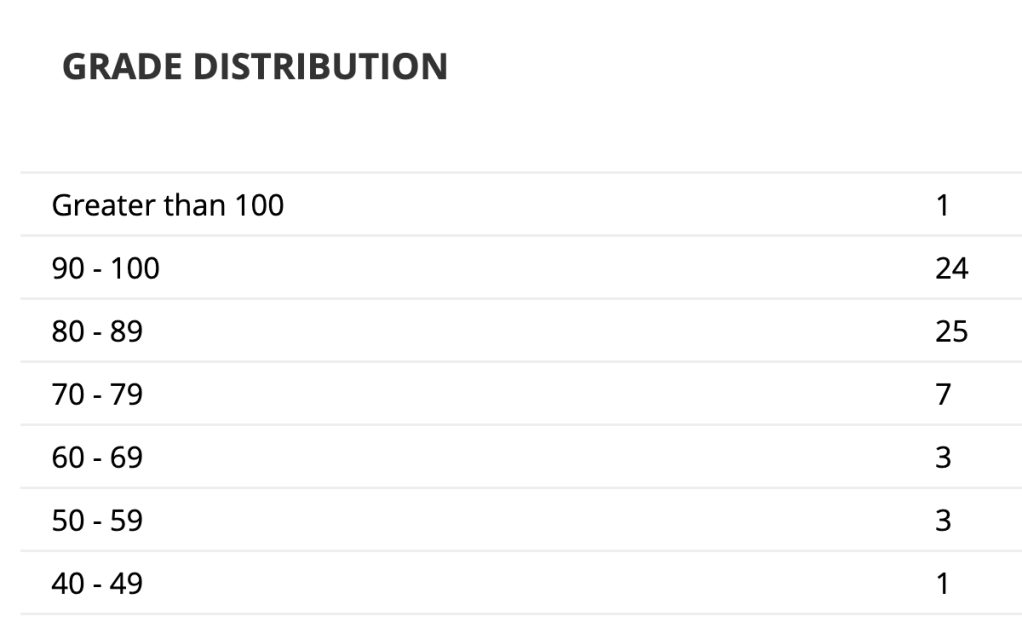
In the last year we have graduated 123 students with BA and BS degrees, 26 MS degrees, and 3 PhDs. While the PhD count is low after last year’s 20, two recent graduates started tenure track professorships, Jie Zhou (MS ’17, PhD ’23) at George Washington University and Michael Chavrimootoo (BS ’20, PhD ’24) at Denison University. Both worked with me on research prior to their successful PhD work – Jie Zhou on secure computing systems, directed by John Criswell, and Michael Chavrimootoo on computational social choice, directed by Lane Hemaspaandra. Michael also runs half marathons.
In technology, this is the year of generative AI. URCS was founded as an AI department, with five AAAI fellows on faculty over the years, including Henry Kautz, who was AAAI President from 2009 to 2014, and Len Schubert, who retired this summer after 37 years on the faculty most prominently in the field of common sense reasoning. The research of over half the department’s faculty is related to AI, with six professors specializing in core areas of statistical AI such as computer vision, natural language processing, graph neural networks, and machine learning theory, and teaching in these subjects. Next year, we plan to hire at least one additional AI faculty member.
We are teaching a large number of students about AI. By my count, in the third week into Fall 2024, the department is teaching ten advanced courses (200 level or higher, 13 of which are cross-listed) to a total of 491 students, including 129 in CSC 242 Introduction to AI taught by Thaddeus Pawlicki; 99 in CSC 245/445 Deep Learning by Chenliang Xu who created the course in 2017; and 23 in CSC 511 Large Language Models, new this year created by Hangfeng He. Additional courses are offered by Data Science and Brain and Cognitive Science and have CS course numbers.
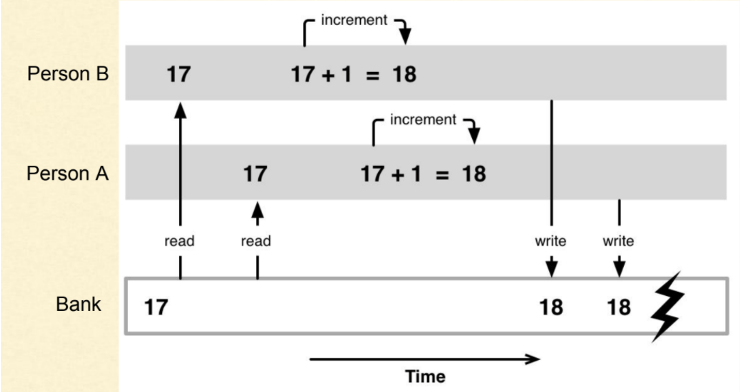
Every year, our undergrads compete in the International Collegiate Programming Competition (ICPC). This year’s lead team consisting of Zeyu Nie ’24 (computer science and applied math), computer science master’s student Xiaoou Zhao, and Yan Zou ’27 (computer science) placed third in the regional, behind MIT and Harvard, and 17th in the North American Championship, just behind Michigan and Cornell. Despite competing against primarily schools with vastly larger CS programs, our students won their spot in the World Finals. In national contests, CS junior Cole Goodman won the NCAA Division III championship and qualified for the US Olympics Team Trials. Cole is the first Rochester student to do so since 1988 and the only athlete who has taken my course and learned computer organization and RISC-V assembly programming.
The department continues to work to broaden CS participation. Among the activities, ten students, led by our newest faculty member Yanan Guo, attended the Grace Hopper Celebration in October in Philadelphia, the largest gathering of women technologists worldwide. One month earlier, Fatemeh Nargesian led a ten-student group to San Diego, the largest in the department’s history, to the Tapia Conference, which annually brings together students, researchers, and professionals in computing from all backgrounds and ethnicities.
Last but not least, this is the year of charity giving. Danny Sabbah established the first endowed professorship in Computer Science with a generous $2M donation. Rick Rashid started the CS50th fund with a contribution of $100K. Since September 1, 2023, forty-seven other donors, mostly our graduates and their family members, have contributed a total of $38K. Charity is good for the soul. Intelligence may be mechanized, but the soul is uniquely human. The generous financial support is a confirmation from our alumni and others who care about the department, its mission, and its direction.
All that we do draws inspiration and strength from our alumni and friends. We are grateful for all your support.
With pride and gratitude,
Chen Ding
Professor and Chair